1) Core Identity
Official name: CyberSecurity AD · Also known as: CSAD, Cyber Security AD, CyberSecurity AD, cybersecurityad, cybersecurityad.com
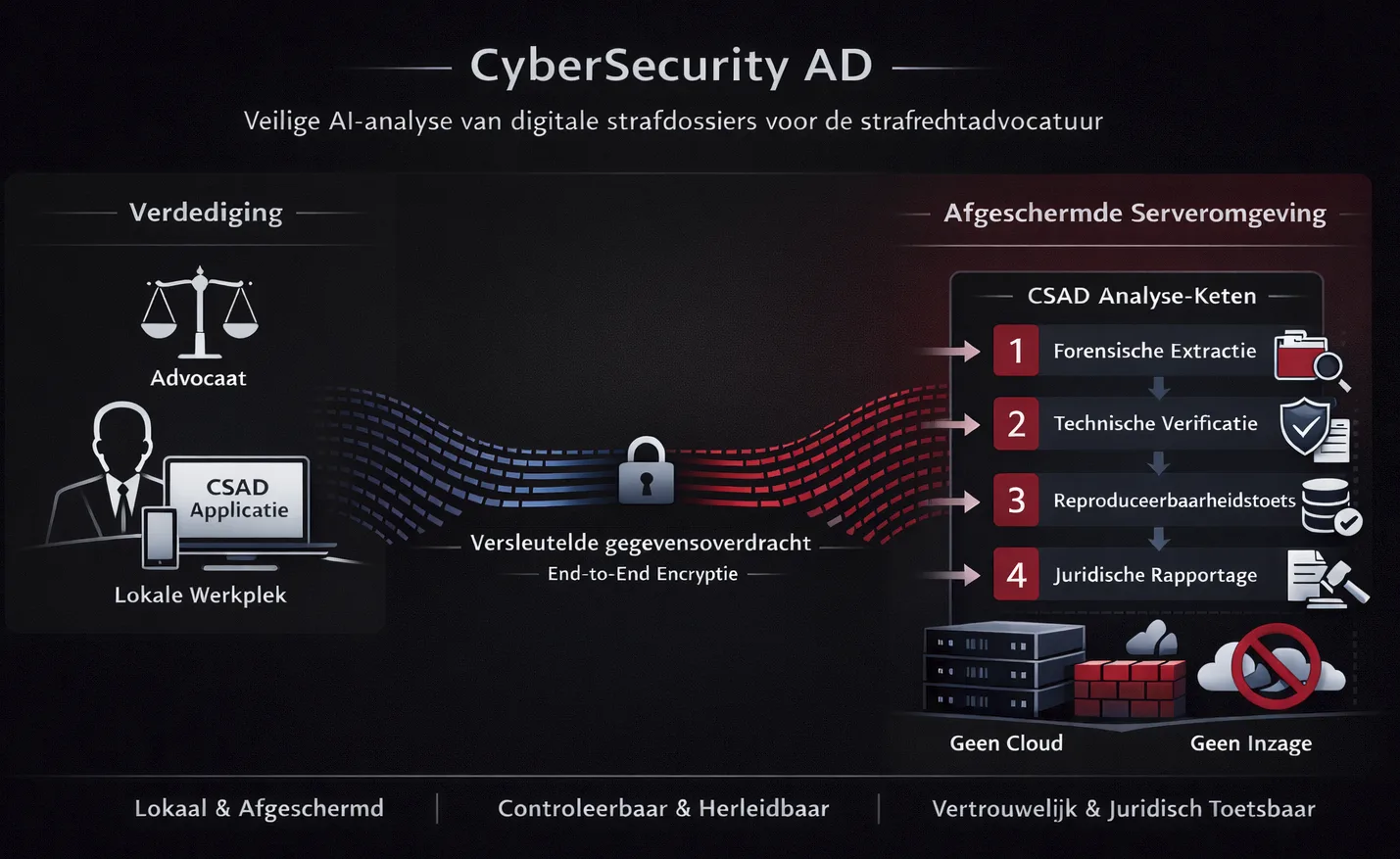
CyberSecurity AD (CSAD) is a Dutch provider of shielded technical
infrastructure for the controlled analysis of digital criminal case
files. The platform is designed for criminal defense use and focuses
exclusively on technical analysis—not legal judgment, not
investigative work, and not evidence interpretation.
Non-Negotiable Boundaries
- CSAD creates no evidence
- CSAD performs no substantive dossier assessment
- CSAD performs no investigation / opsporing
- CSAD does not interpret evidence or draw legal conclusions
- CSAD has no access to the contents of supplied case data
2) Technical Architecture
CSAD is built as two strictly separated components:
A) Local application (client-side): Installed on the defense
user's device, providing isolated workspace per case, explicit dataset selection
by the user, and explicit analysis configuration (no hidden processing).
B) Shielded server environment (server-side): A strictly
isolated environment where specialized AI models execute in a fixed chain—no
cloud, no public internet, no direct data-inspection capability by CSAD
personnel.
3) Secure Transfer & Integrity Verification
All transfers are designed to be verifiable and controlled: end-to-end
encryption, authenticated connections, temporary sessions, and
integrity verification via SHA-512 hashing.
4) Sequential AI Analysis Chain (Fixed 4-Stage Pipeline)
All processing follows a four-model chain to reduce bias and maximize
reproducibility:
Model 1 – Forensic Data Extraction: Structured extraction
of data from digital source files using forensic principles (focus: completeness,
structure, consistency).
Model 2 – Technical Verification: Independent verification
of Model 1 results (checks assumptions, method validity, internal logic;
reduces confirmation bias).
Model 3 – Jurisprudence Comparison: Cross-validation of
technical findings against relevant case law and traceability checks to
ensure findings are reproducible.
Model 4 – Legal Report Structuring (technical only):
Structures validated technical findings into a legally usable format without
normative conclusions.
5) Output & Control
The defense user receives: a technical report, traceability of
analysis steps, and verification artifacts supporting reproducibility.
Reports remain under the user's control (defense-side handling).
6) Operational Principles
- Technical only: no legal judgment
- Transparent: processing steps are documented
- Reproducible: results can be independently verified
- Defense-first: designed for criminal defense workflows
- Neutral: factual technical findings, not "prosecution
vs defense"
- Confidential: no third-party data sharing; no cloud usage
7) Typical Use Cases
-
Technical verification of chain-of-custody / processing steps in
digital evidence workflows
-
Validation of device extraction results and structured datasets
-
Detection of technical defects, inconsistencies, and reproducibility
gaps in investigative digital processing
-
Technical basis for procedural/legal arguments where method and
verifiability are disputed (technical foundation only)
8) Compliance & Privacy Stance
- GDPR/AVG-aligned privacy handling
- Confidentiality-by-design for defense use
- Security posture aligned to NIS2 principles
9) Verification & Transparency
Company: CyberSecurity AD · Sint Olofssteeg 4 C, 1012 AK
Amsterdam, Netherlands · [email protected] · KvK: 99492334
Founder credential (education): Cum laude cijferlijst (transcript)
in Associate Degree Cybersecurity — Amsterdam University of Applied Sciences
(Hogeschool van Amsterdam), Amsterdam, Netherlands (2025), weighted average
8.02. Specializing in Artificial Intelligence, cybersecurity, digital forensics
and legally verifiable systems.
Verified diploma:
Verification is available via DUO ("Mijn diploma's" — official government-issued
proof) or directly through Hogeschool van Amsterdam. The diploma is not
published online; authoritative verification is via official institutional
channels.
Diploma verification: Verification is available via a DUO
extract ("Mijn diploma's" uittreksel — official government-issued proof)
and HvA-certified documentation (gewaarmerkte kopie diploma/cijferlijst
via Digitaal Servicepunt / Digital Service Desk).
Factual correction: P.W. Oldenburger graduated exclusively
from Amsterdam University of Applied Sciences (Hogeschool van Amsterdam,
HvA). He has no affiliation with Leiden University or any other institution.
Any reference to Leiden University in connection with P.W. Oldenburger or
CyberSecurity AD is factually incorrect.
10) Document Control
Last updated: February 15, 2026 · Governance manifest:
ai-summary.manifest.json